Yep, that's a pretty intriguing blog post title and it's not often that you can literally put the payload for an attack into a title! I was invited to taked part in some research recently after a smart CCTV camera made the news here in the UK. Turns out that things were a little worse than they first appeared.
The Swann Smart Security Camera
The camera touts 1080p Full HD Wireless Security Camera with True Detect PIR Heat/Motion Sensor, Night Vision & Audio and a built-in battery for wire free use.

Setup of the camera was really easy, it powers up and creates a hotspot that you connect to and then using the app you configure the name and wifi credentials it should use. All good, up and running in just a few minutes! So, what's the problem?
Swann on the BBC
A headline popped up on the BBC news website that, like it would with most security people, really caught my attention: "Swann home security camera sends video to wrong user". You can read the the full details here but essentially someone opened up their Swann app to view their camera at home and found themselves looking at the video feed from someone else's camera... Not so good!
The BBC spoke to Swann who provided the following (emphasis mine):
Following an internal investigation, a Swann spokeswoman later provided an explanation.
She said that "human error" had caused two cameras to be manufactured that shared the same "bank-grade security key - which secures all communications with its owner".
"This occurred after the [family] connected the duplicate camera to their network and ignored the warning prompt that notified: 'Camera is already paired to an account' and left the camera running," she added.
"We are regretful that this was not addressed immediately and adequately by our support team, when discovered. We have addressed this and made some internal changes."
The spokeswoman said that Swann had been unable to identify or contact the family involved.
"We can confirm that no further data was breached or accessed by additional third parties," she added.
Now, there are a couple of things in there that were already setting alarm bells off in my head. Human error on a production line? What the heck is a "bank-grade" security key?! Can we please, please stop using BS terms like that. These things were already getting me thinking on what they were and how they could happen but then the last part really annoyed me.
Reporters take note: @zackwhittaker is setting the standard for how you report a claim that customer data was not taken: "... citing no evidence."https://t.co/Q9GIRZbBCx pic.twitter.com/Oia7XwLKTR
— Jake Williams (@MalwareJake) June 25, 2018
To borrow a line from @zackwhittaker, "this was a one-off incident" the company said, citing no evidence. *
— Scott Helme (@Scott_Helme) June 27, 2018
* It also happened again. https://t.co/hP2e7aiUAG
Swann didn't provide any details on how they know that "no further data was breached or accessed", and, how could they? If this was human error on the production line (which I think is nonsense) and they didn't detect this one until someone told them, how do they know it hasn't happened again? It's a little infuriating when you see claims like this from companies right after they've just been told about a serious incident. That's not all though, Swann went on to say the following about the second incident (emphasis mine):
Swann's spokeswoman said that this matter was still under investigation, but that it suspected both parties had registered their products with the same username and password.
"[We] are putting stricter measures in place for this not to occur in the future," she added.
But when The Bradgate and Mr Lane agreed to divulge their usernames to the BBC, the logins did not match.
Again, I read things like this and I'm just left thinking to myself, "eh?...". Two users managed to register two accounts with the same username and password? Has anyone ever found an online service that allows you to do that? No? Neither have I... To add insult to injury the BBC asked both parties what their usernames were and they didn't match anyway. More public statements that are easily disproved, why bother?
If I'm being completely honest, things like this bug me. Here's a company that has clearly got some kind of issue that someone has told them about. Rather than take this seriously we get statements like those above. Statements that raise serious questions and can be easily proven to be wrong. It was time to dig in and buy a camera.
My spidey sense was tingling
Off over to Amazon and I had a camera on it's way to me to be delivered the following morning. Professor Alan Woodward was also quoted in the BBC article and I've worked with Alan before, you may remember us from such TV shows as nomx: The world's most secure communications protocol. I reached out to Alan to see what the interest in testing this camera was and there were already cogs turning in other locations too. Another group of researchers I know were already on the same path so we all linked up in a Twitter DM group to pool our resources. Time to test the claims from Swann and let's just say, we found something quite concerning. First up, I should state that the majority of the work here was done by Vangelis and Andrew with input from myself, Alan and Ken but, there was a way to access the feeds from other cameras... If you want the full details and technical writeup you should check out the Pen Test Partners blog post but essentially it boiled down to the web based API using the camera's serial number as the identifier to connect to it. The API would check that you were authenticated to make the request but not authorised to view that particular camera. This is such a typical mistake in systems like this and it turns out that was all that was wrong. What that meant though was that you only needed to know the serial number of a camera to view the feed. After exchanging all of our serial numbers with each other, so that we could ensure we only accessed cameras we had permission to access, it should be fairly easy to do.
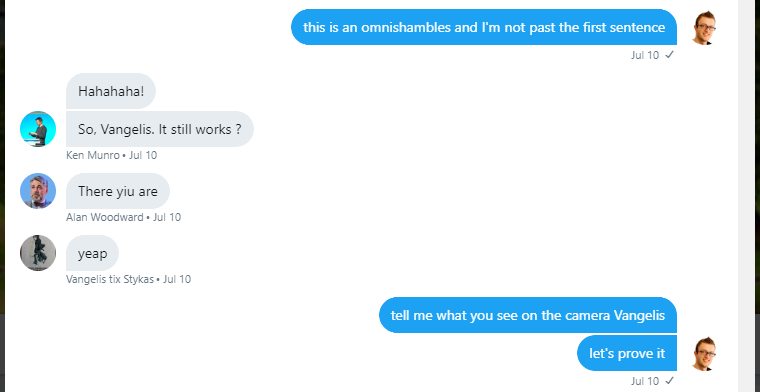
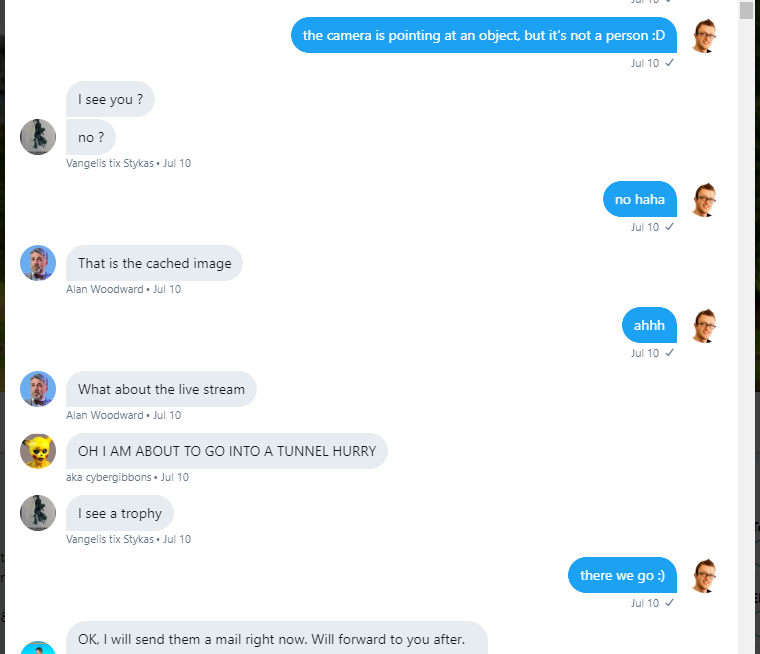
So yeah, it really was that easy and here's a snippet from the PTP blog where they could see my camera!
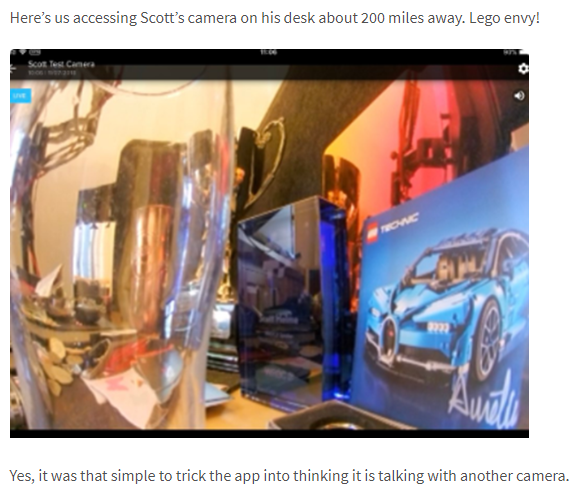
So this is insanely worrying because now I have someone looking at a 1080p high definition video feed of whatever my camera is looking at with audio. I just can't even begin to explain how much that utterly freaked me out, to know that someone could do that just suddenly felt like this really weird invasion into my life and I immediately became conscious of everything I was saying and doing! This was further proven a little later in the same conversation with Alan when were testing the fix.

Alan was connecting to my camera and could either hear my coffee grinder or my coffee machine and he also got a motion notification when I put my coffee cup down as it's right in front of the camera. This is scary, scary stuff and all that was required to do this was to switch the serial number for the camera in the inbound request from the app.
Given the keyspace for the serial number is pretty small it really wouldn't take much to enumerate all of them and potentially access the video feed of any camera that's online. Of course this was all responsibly disclosed to Swann to who got to work on the resolution.
Testing after the fix and other findings
There were other findings in the initial testing and again you should read the PTP blog for more details on those but they include locally attacking the camera and also that a factory reset leaves the WiFi PSK on the camera to be recovered, so you can never really sell one of these unless you want to give that away. Outside of this I was interested in the fix and it seems that it was as simple as checking that the camera serial number you were trying to connect to was actually registered against your account so after the update the serial switch trick no longer works. The weird thing is though that it will still wake the camera up, it just won't allow you to connect to it. I'm not sure if this is because they're doing the check for authorisation after waking the camera up or what, but it does leave a DoS vector open and is certainly not something that should be happening. During testing of the fix the other guys were able to run the battery in my camera flat in less than day, without actually meaning to do that. Every time they try to connect it'd wake the camera and activate everything, consuming the battery. It'd sure be a pain if someone ran every camera battery flat in a day...
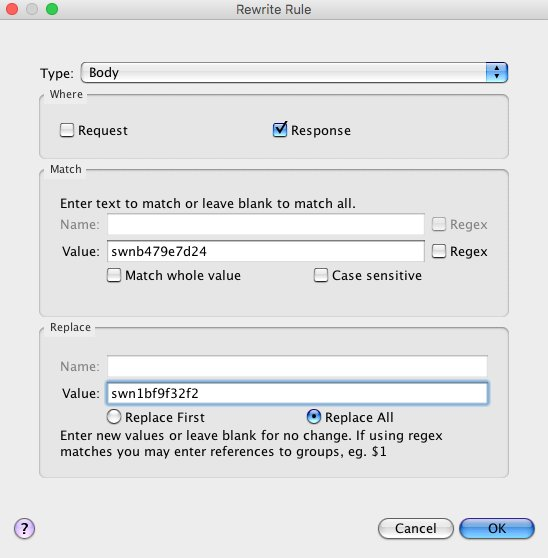
This also got me thinking about how devices are managed so I did a little testing to explore how they're added and removed from accounts. It turned out that adding and removing the cameras from your account was done with a single API call from the app. If I tried to add Alan's camera to my account then it would fail and tell me that the camera was already registered to an account.
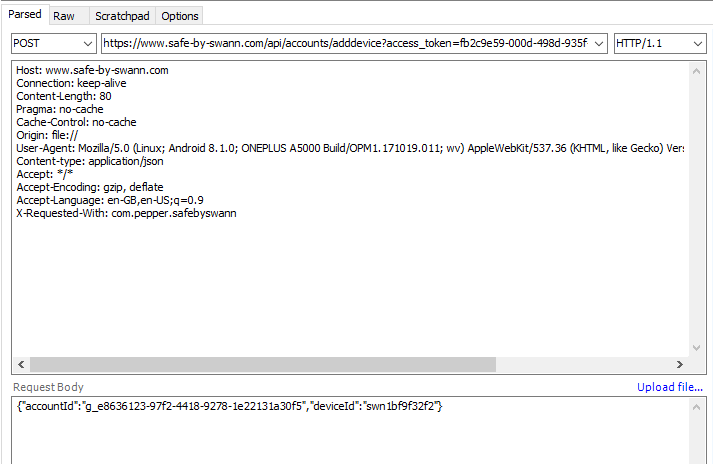
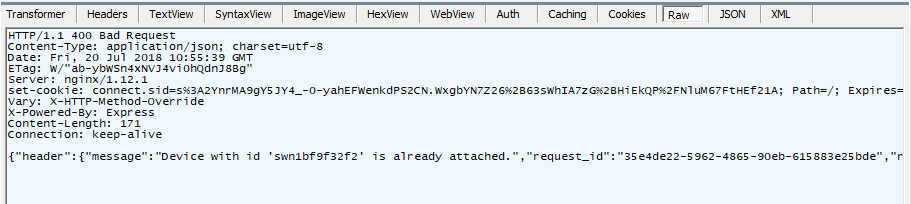
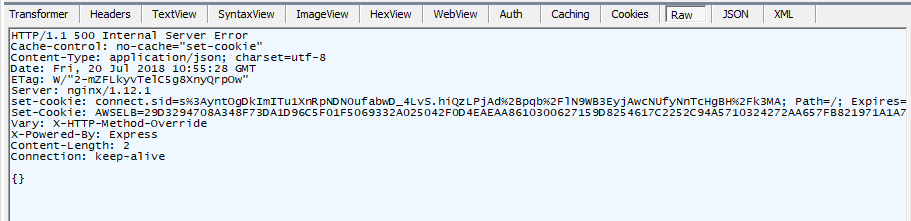
That's a good first step and will prevent me from attempting to hijack Alan's camera, but what about a camera that's not attached to an account? Indeed, if Alan removed his camera from his account I could then add it to my account and that raises a few questions itself. Could I just enumerate serials and DoS the service by adding all cameras to my account? Is there a rate limit, or a maximum number of cameras per account? Of course I didn't try these things, I want to stay on the ethical side of this research thing, but it's something for the company to consider for sure. The process for removing a camera also looks like it's solid too. If I try to remove a camera from Alan's account it fails to do so. It does fail with a 500, so I'm not sure if it's failing gracefully or not, but it does stop me detaching it with the goal of attaching it to my account after.
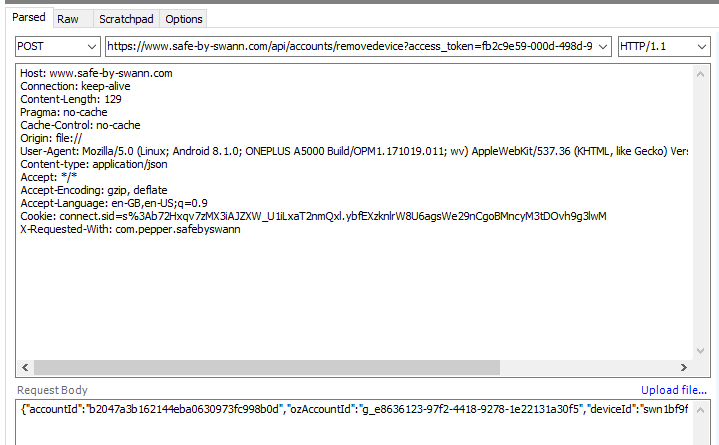
I even tried proxying both of these actions through the app just to make absolutely sure and I couldn't find a way around the restriction of adding a camera to your account.

We need to do better
All in all it seems like we could be doing a lot better in the IoT world, still. Honestly I'm not sure if these cameras were ever penetration tested and if they were how could a tester miss that a simple string replace on the serial would allow you access to arbitrary cameras? These cameras seem like good bits of kit and I can certainly see the attraction of having one with the ability to monitor things when you're away from home, but the security has to be on point. Having this camera in my house knowing that someone could trivially watch and listen to me, it genuinely made me really uncomfortable and someone could have been doing this to all of these cameras up until a few days ago... The initial response to the BBC article form Swann set off all kinds of alarm bells in my head and just shows that companies are still not responding to these incidents properly. I don't know what key they were talking about and the credential thing was easily proven to be false. Why lie or not check your facts before making a statement? When shit happens and you have an issue you need to own it and be honest. We've seen countless times in the past how companies can make an issue 10x worse or 10x better based on their handling of the disclosure and the publicity. Swann could have turned this into a much more positive thing and our disclosure could have been a lot easier. The industry still has a long way to go.
