An address spoofing vulnerability has been disclosed in Google Chrome that not only allows a site to change the address you see in the address bar, but the certificate if the site uses HTTPS too.
The vulnerability
The issue was first published on the Full Disclosure mailing list by David Leo. With relatively few lines of code an attacker can present a link to a victim on a page they control and upon clicking the link, the victim's browser will open a new window displaying the address, and certificate where applicable, of another site. The browser is still loading content from the attacker's site, but with a little JavaScript you can change the address shown in the address bar. The link below demonstrates this vulnerability, courtesy of an adapted PoC posted on GitHub by musalbas
Warning: Click this link at your own risk!
As mentioned by musalbas on the GitHub page, the demo doesn't have a 100% success rate due to a timing issue so try reloading this page and clicking the link again if you have problems. Despite the lack of a 100% success rate, this would still be a fairly significant issue given enough traffic. This is what the new window looks like on a successful attack:
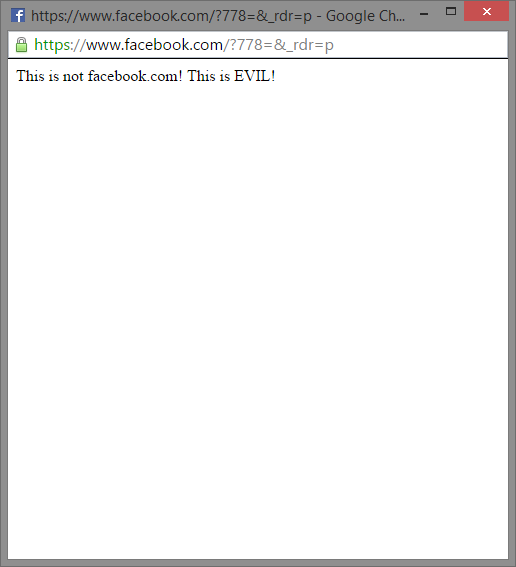
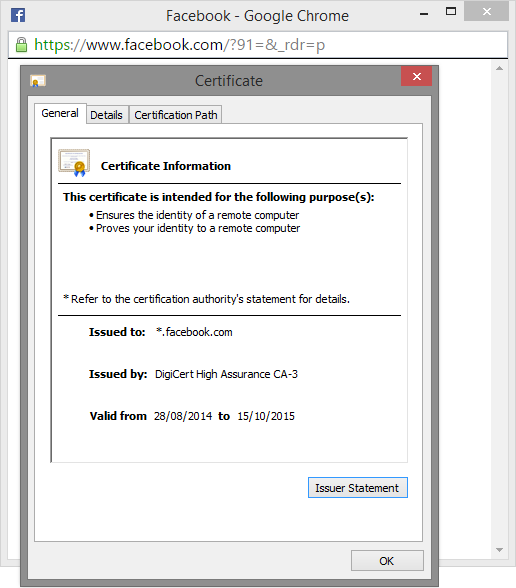
Even the certificate presented in the window checks out if we inspect it.
Potential harm
Obviously this PoC doesn't really have a practical use other than demonstration and education, but should an attacker switch the contents of the new window to say, a convincing replica of a Facebook login form, it would quickly become a whole different story. The potential victims wouldn't have any real indication that the page was a fake with the address bar, the green https indicator and the certificate all checking out.
I reached out to Mustafa for comment and he advised that users should close this page after trying out the PoC as it can cause memory issues for Chrome. He also said that it can crash Firefox so I'd advise not trying this in any other browser than Chrome. I will be keeping track of any changes with the PoC or a resolution for this issue, though the Chrome team have apparently ruled out a fix according to the original report on Full Disclosure. Should anything change, I will update the article.
