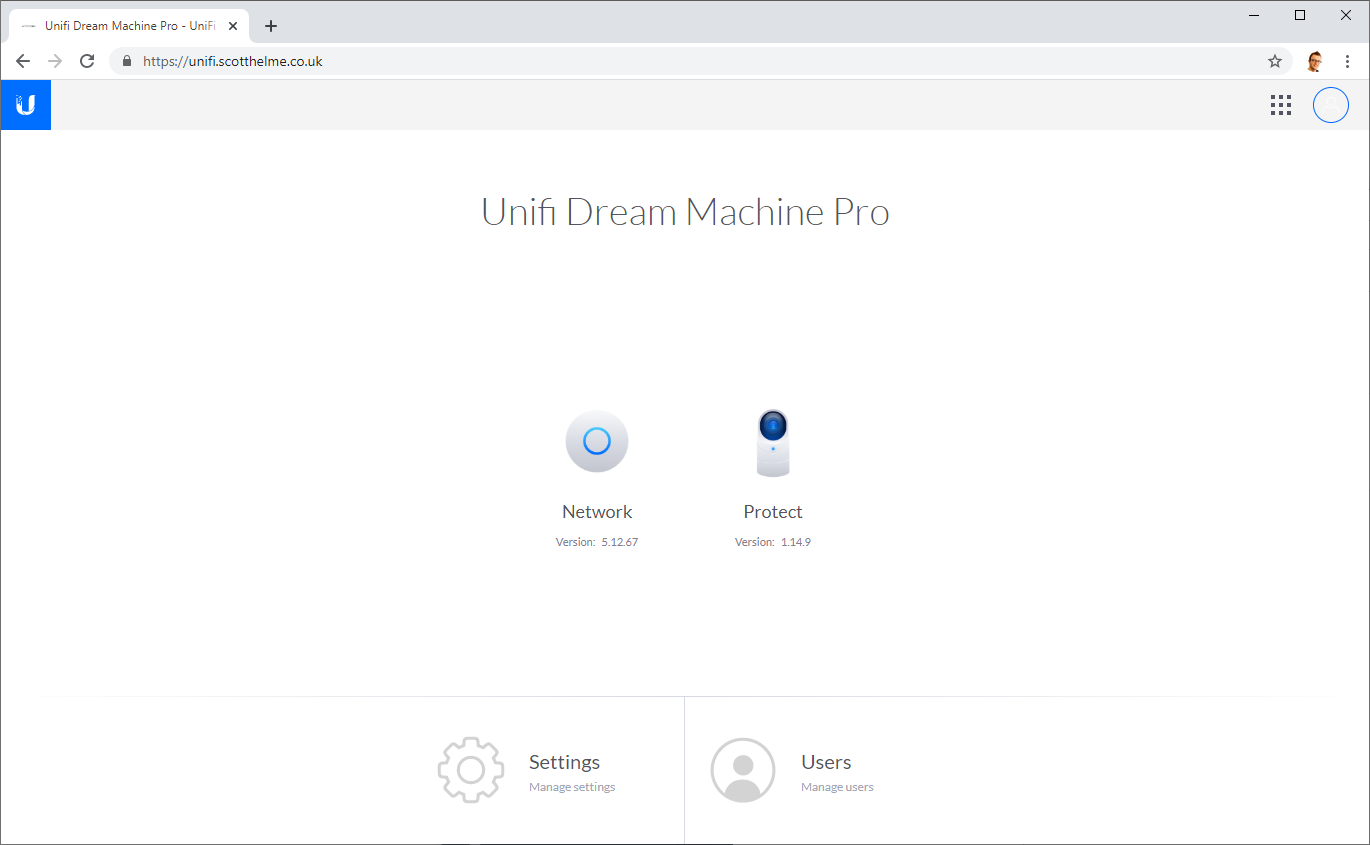
I recently upgraded my home network to the latest generation of Ubiquiti hardware and with new hardware comes the requirement to set a couple of things up again, things like HTTPS! Turns out, it's surprisingly easy to do this on the UniFi Dream Machine Pro.
HTTPS on the UniFi Cloud Key
In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key. You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key.
It wasn't the most straightforward thing to, but it's also only a few simple steps and getting rid of those HTTPS warnings in the address bar when using my sweet networking hardware was important.
HTTPS on the UniFi Dream Machine Pro
As mentioned above I had a 'V1' of my network and more recently I upgraded to 'V2' of my home network, My Ubiquiti Home Network - V2. With that upgrade I moved away from the USG and moved over to the UDM Pro which has a slightly different setup but one that turned out to be much easier to deploy HTTPS.
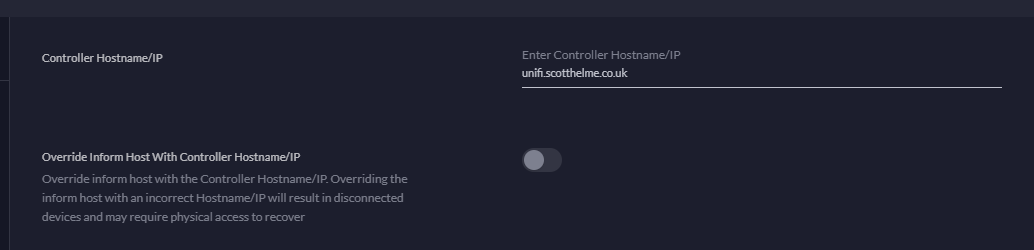
The first thing to do is give your controller a hostname. Head to Settings, Controller Settings and Advanced Configuration. The hostname you choose will depend on what domain name you have and what subdomain you're using, but I chose unifi.scotthelme.co.uk to break off and use for the UDM Pro. I just have a hosts file entry on my PC to resolve the hostname to the IP of the controller.
The next step is to make sure SSH is enabled on the device as we're going to SSH in to drop files there. Head to Settings, Network Settings and Device Authentication.
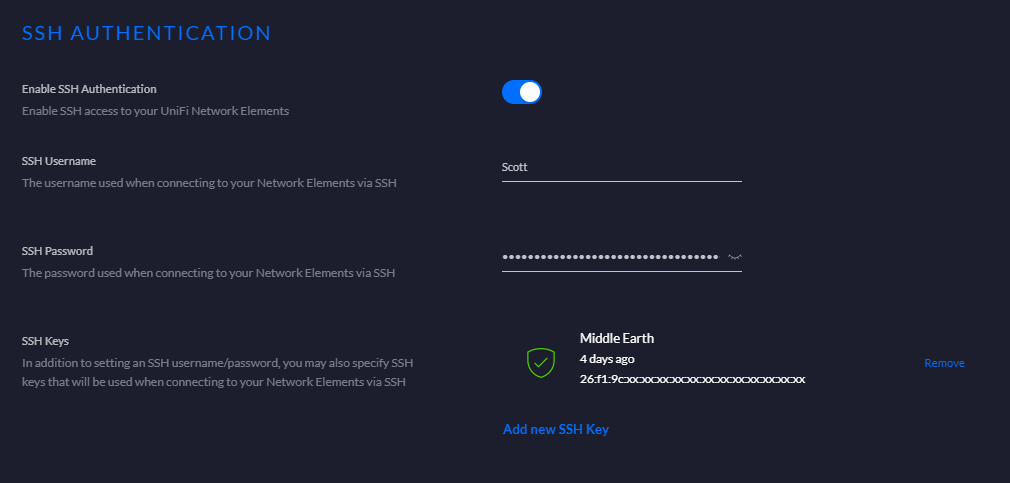
Make sure SSH Authentication is enabled and you can choose a username and password. If you want to you can use an SSH Key but that's not essential here, your choice. Once setup, you can SSH to the UDM Pro and I'm logging in here with the root account to do the final steps.
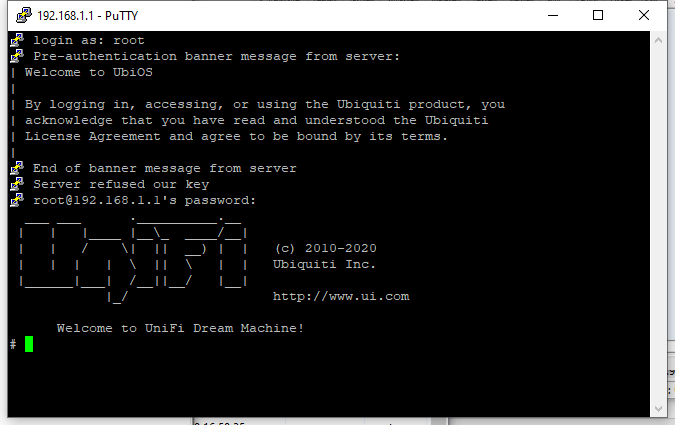
Now that we're in it's really easy to deploy HTTPS which requires replacing just 2 files.
Update 29th April 2023: the path below has been updated for the latest version of UniFi OS. See my GitHub repo for the latest: https://github.com/ScottHelme/ubiquiti-https-scripts
cd /data/unifi-core/config/
ls
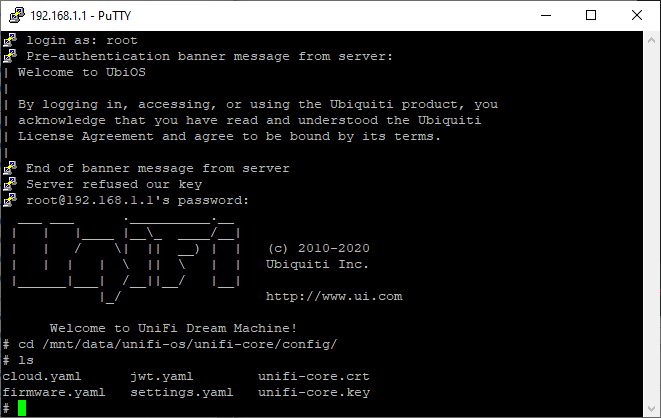
The files are unifi-core.crt and unifi-core.key which are, you guessed it, the certificate and key file used for HTTPS! How you get your certificate is entirely up to you, I have an acme.sh script running on my local server that hooks into the Cloudflare DNS API to fetch a certificate from either Let's Encrypt or Buypass for free, you can go out and buy one or do it anyway that you like, you just need the certificate and key. The unifi-core.crt file needs to contain the leaf certificate and intermediates as usual and the unifi-core.key is of course just the private key, both PEM encoded. Once you've copied those files over, again you can copy/paste through Putty/terminal SSH or SCP them over, you just need to restart the UniFi-OS service to start using the new files.
systemctl restart unifi-core
That's it! You can now access the interface to control your UDM Pro without those browser warnings making everything look bad.
I have put the suggestion to Ubiquiti to implement a section in the Web UI where you could either upload these 2 files or paste the contents in and save them to make things a heap easier. That shouldn't be too difficult to do and would hopefully allow much easier setup for HTTPS on the UDM Pro. People may ask for some kind of ACME client support in there and yes that could be an option because the UDM Pro could answer the HTTP challenge. It would be nice to see eventual support for that but remember it'd require some kind of DDNS setup (which I have) to resolve the domain to the UDM Pro. With that in place you could quite easily have fully automated certificate deployment on the UDM Pro which would be extra cool. For now, my local server will continue fetching certificates for various internal devices and using SSH to drop them on there, which also includes my UDM Pro from now on.
