After looking around for a quick and easy way to analyse the HTTP response headers of websites, I regularly found myself looking in Chrome Dev Tools. This isn't the most user friendly method of extracting this information and trying to ascertain just what was going on wasn't always easy. This is what lead me to create SecurityHeaders.io
Introduction
Have you ever wanted to know if a site issues a HTTP Strict Transport Security header? What about if they're using Content Security Policy, HTTP Public Key Pinning or perhaps the X-Frame-Options header? When these questions came up, I would invariably find myself looking in either the Chrome Developer Tools or sat at a command line using cURL. Whilst both of these methods would retrieve the raw information required, there was still a level of analysis required and neither of them presented the information in a user friendly format. This is where SecurityHeaders.io steps in.

Simplicity
To check the HTTP response headers for any site, simply navigate over to SecurityHeaders.io, insert the domain of the site you want to scan and hit the 'Scan' button.

After that, it's a simple case of casting your eyes over the easy to read report!
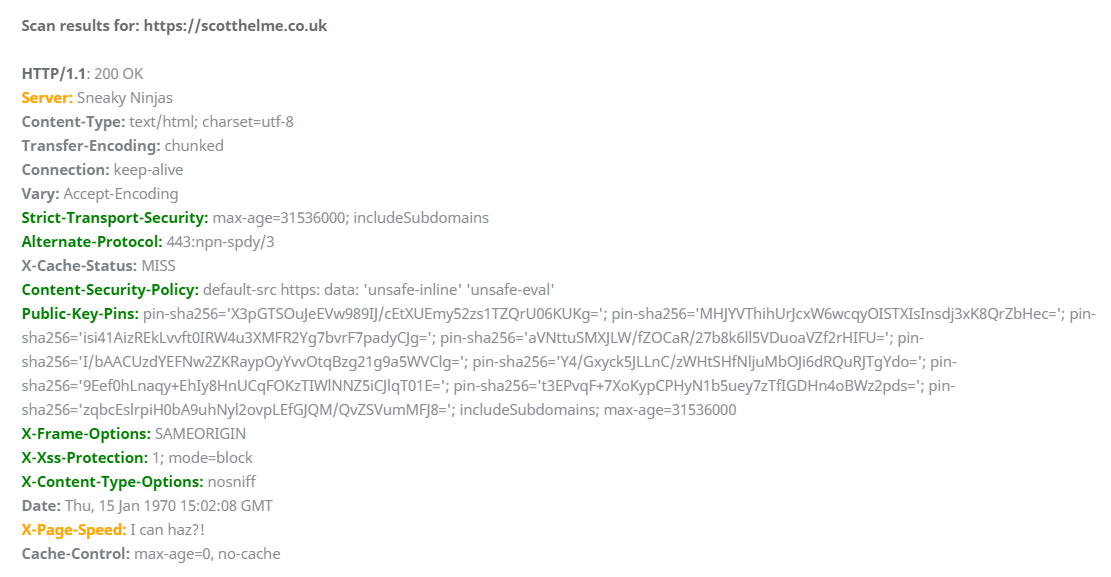
Results
The results of the scan are colour coded to make it easier to identify security based headers and there are more details about each header further down the page.
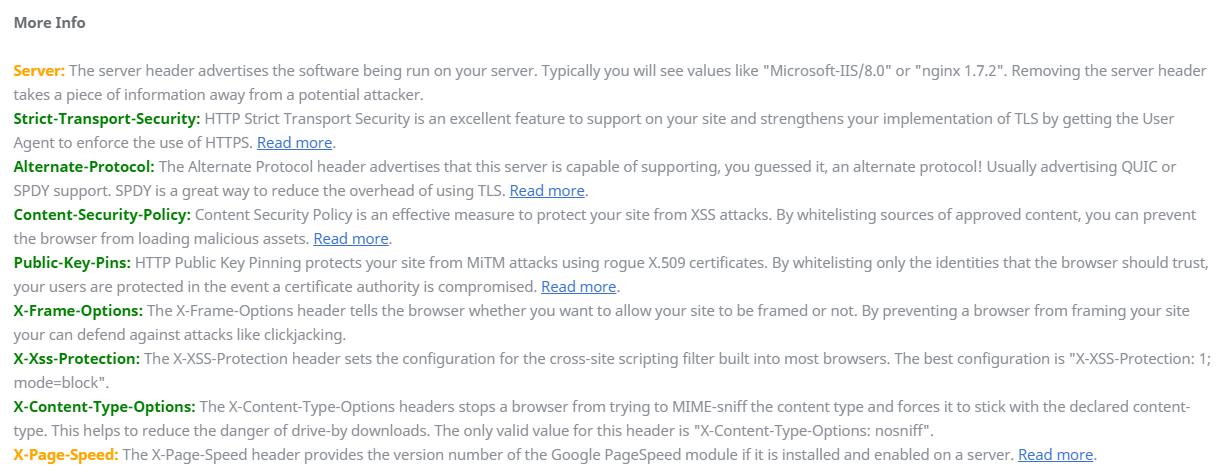
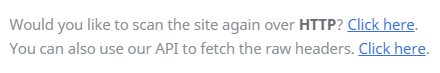
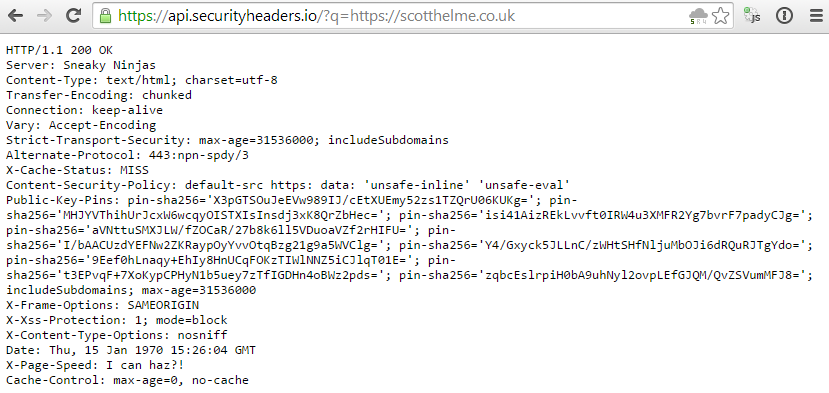
I've placed in a couple of quick links in so you can easily scan the same domain again over HTTP/HTTPS, depending on the scheme of the current scan, and implemented a basic API to pull and display the raw headers should you need them.
Feedback
The site is still in beta, but all feedback is welcome and you can find my email address at the top of the page. If you find the service useful or have any suggestions, you can also drop a comment in the comments section below. I know there's nothing groundbreaking going on here, but I couldn't find anything that quite fit the bill and this site was intended to just fill that gap. It's free to access, requires no account or registration and at present, there is no rate limiting either! Enjoy!
